
Consumer
How to avoid identity theft if your phone gets lost or stolen in Malaysia
over 6 years ago UiHuaWhether left behind in the bathroom or having the phone snatched from their hands at a sidewalk (both happened to this writer’s friends btw), we all know someone who’s had their phone lost or stolen – or even personally experienced this ourselves.
Off-hand, you might just assume that your poor phone is probably being sold or salvaged for parts… but you may want to think again.
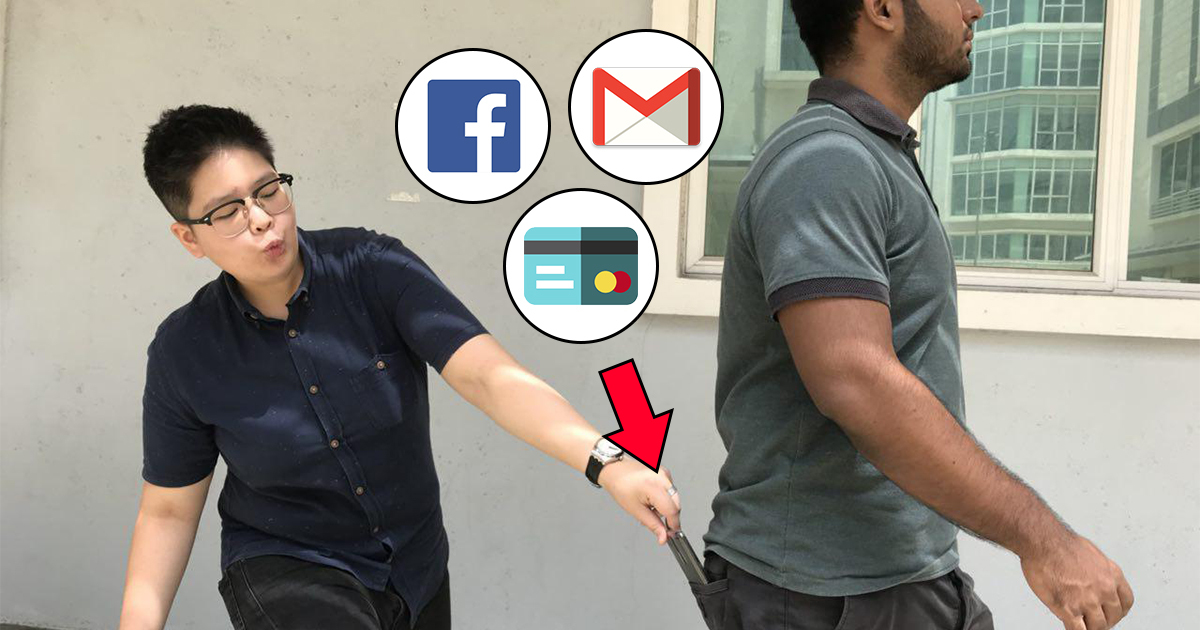
We’ll bet that at the time you’re reading this, your phone is logged in to your email and social media accounts at the very least. This means that if the person who found or stole your phone has more ambitious intentions than just selling it, you’ll be in for a whole lot of headaches and heartaches.
Basically, this means that someone with access to your phone also has access to all the information and accounts stored in it.
In other words, contact information can be copied and sold, photos can be compromised, social media and email accounts can be hijacked, and so on to the point that, perhaps, even arresting the hijacker and retrieving the phone cannot undo the damage caused. While we could go into the laws on how this might be illegal and what punishments the thief/hijacker can face, what’s more important is noting that, for the most part, the damage is already done.
Thankfully there are some measures that can be taken to prevent this from happening, and these apply whether you’re on iOS or Android.
1. Use a pin-protected lockscreen

While nothing beats the convenience of instant access to your phone, a lockscreen will provide the first line of defense. It’s important to note that lockscreens can be quite easily bypassed regardless of iOS or Android (Google it), so it’s more of delaying access rather than an all-and-out solution.
If you’re on Android, note that using a Pin is way more secure than using a Pattern. In fact, someone is 64% more likely to figure out a patten code after seeing you do it once, compared to 11% on a Pin code. Of course, this won’t be as relevant if you use a fingerprint scanner or Face Unlock.
Either way, the reason you want to delay someone from accessing your phone is because…
2. You can remotely Lock/Wipe/Locate your phone
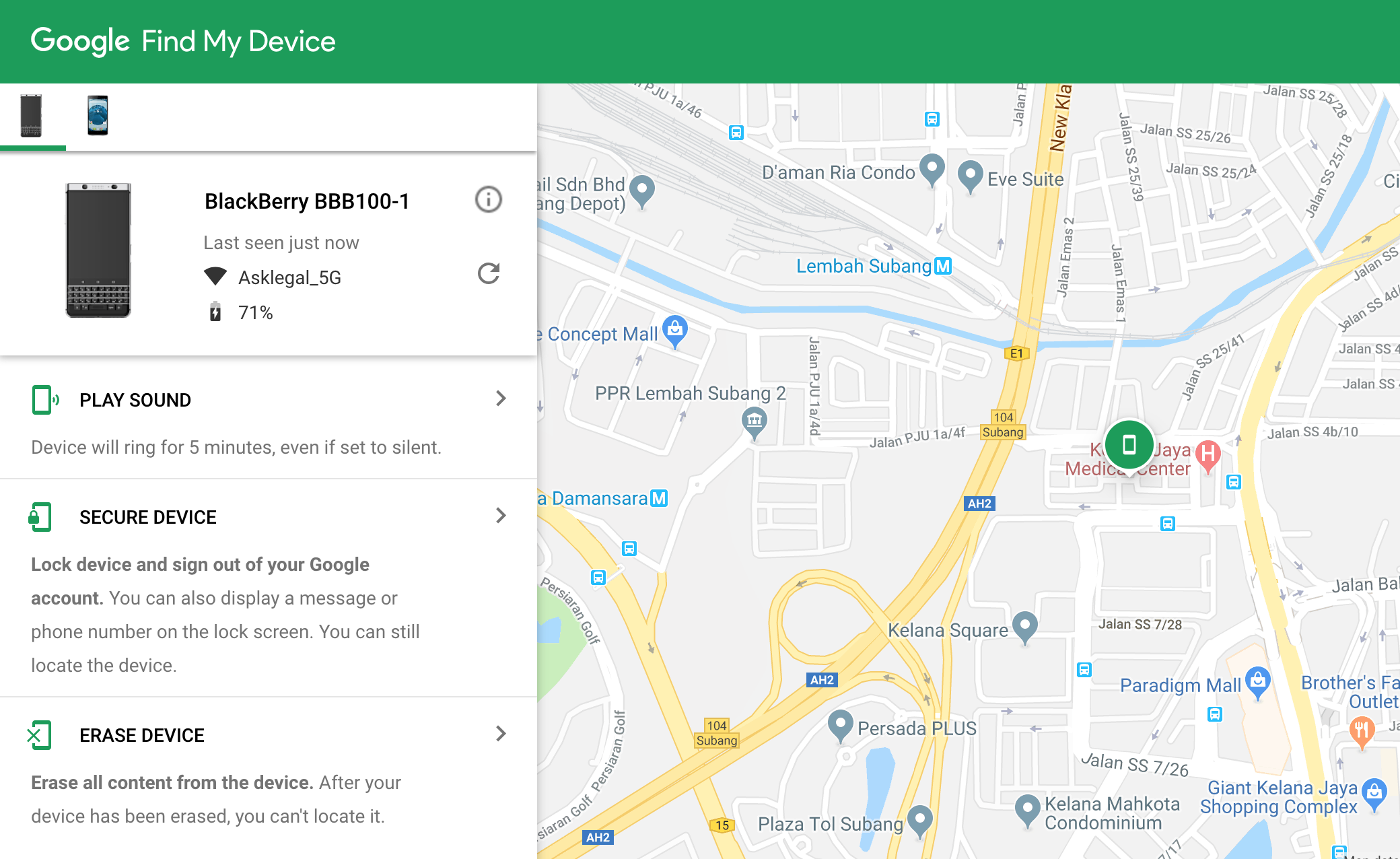
Both Apple and Google have released official apps to help you manage a lost or stolen phone – Find My iPhone for iOs and Find My Device for Android. For the most part, phones will come with the apps pre-installed, but make sure you have them set up and activated!
Essentially, the moment you realize that your phone is missing, you’ll have to:
- Get access to another phone or computer.
- From the browser, access the desktop version of the app – Android link here | iPhone link here
- Sign in to your Google / iCloud account. You can also login to the app from another phone if the owner gives permission.
Here, the features slightly differ from iOS to Android, but both essentially allow you to do the following:
- See your devices’ current location – If you’ve misplaced your phone
- Make your device play a sound and display a message – If you’ve misplaced your phone or want to annoy the thief
- Lock your device and log out of important accounts – To be used if you think your device is still retrievable
- Wipe your device – This is the “nuke” option. Activating this will completely erase data on your phone and restore it to factory settings
One thing to note is that some of these features may not work if you have disabled certain features like GPS or if the phone is in power-saving mode. However, remote locking or wiping will take effect as long as there’s a data connection (or once data is reconnected).
If you’re able to locate your phone and want to get it back, notify the police and ask them to escort you – don’t do it alone!
It’s best that you enable these features on your phone and take a moment to familiarize yourself with them – just remember that testing the Wipe function will actually wipe your phone so don’t say we didn’t warn you!
Also, if you’re borrowing someone else’s phone or laptop, don’t forget to log out.
2a. Encrypt your phone
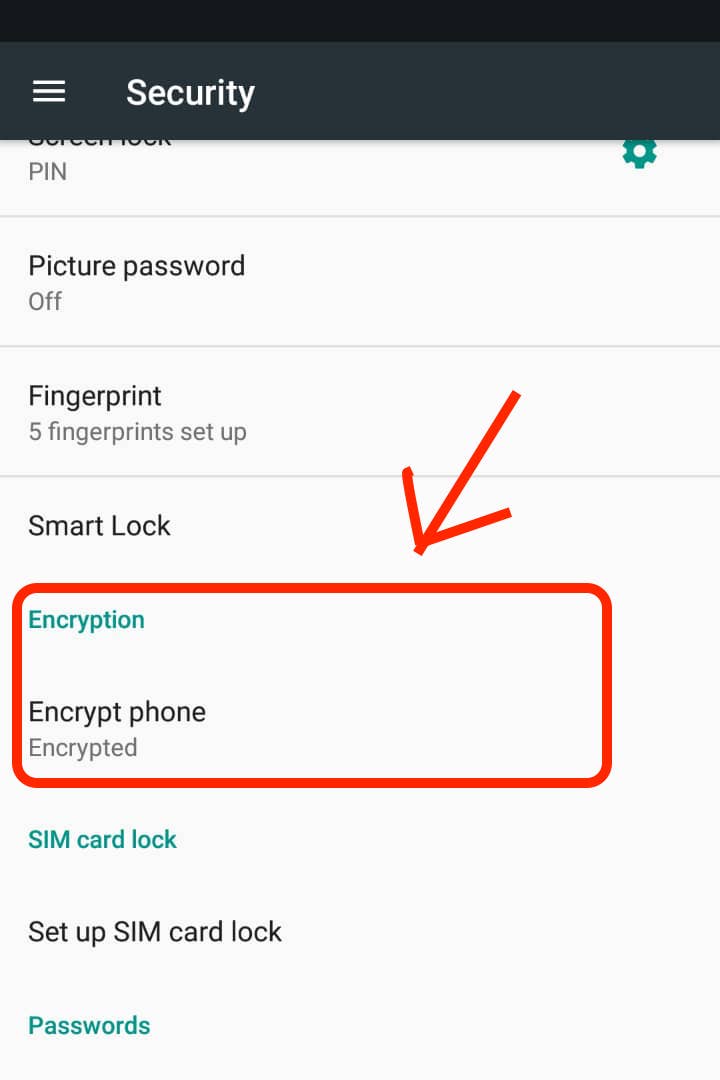
Encryption may sound super technical (and it is) but, for purposes of this article, you can consider it an optional delaying tactic. The idea behind this is that the person who finds/steals your phone may turn it off so you can’t remotely track them. An encrypted phone will add another barrier between their grubby fingers and your private information when they turn the phone on again.
On an iPhone, encryption is automatically enabled the moment you’ve set up your PIN number/Touch ID. It’s recommended that you enable the option to wipe the device after 10 failed attempts to unlock it.
On Android, encryption is not usually enabled by default. Because there are many versions of Android in the market, some manufacturers may not include this feature or may rename it. Usually though, it can be found under the Security settings.
3. Change your passwords ASAP
If someone has access to your phone, they can just as easily change your passwords to lock you out of your own accounts. If that happens, you’re either going to say goodbye to your emails/friends/followers, or begin the arduous task of reclaiming your accounts by confirming your identity.
Changing passwords will immediately log you out of the particular account. Remember to do this for your email accounts as well, because a hijacker can easily tap “Forgot Password” to regain access!
Also, no matter how forgetful you are, NEVER note down your bank account PINs or online banking passwords on your phone!
4. Tell everyone that you lost your phone
Feel free to rant and gripe about your lost phone or the state of Malaysian society to your contacts – but the main point is to give them a heads-up that there could be someone else using your accounts, and they should ignore any messages or requests for the time being.
Unsuspecting family members or friends can unwittingly end up parting with sensitive information or be scammed out of their money.
Prevention is better than cure
Again, the law can only go as far as retrieving your physical phone or give you the satisfaction that justice is delivered if the thief gets arrested. But the law cannot get your accounts back or completely remove any photos or information leaked online. As an example, hundreds of private photos of celebrities that were leaked online in the 2014 iCloud security hack (also called The Fappening) remain online and discoverable to this day despite numerous takedown requests and even a lawsuit against Google to remove them from their search engine.
So just like how you’d take measures to prevent someone from robbing your house, the same can be done to your phone following the steps above. As an additional security note, it’s also a good idea to perform a factory reset on your phone before you discard, sell, or send it in for repairs.
If you’re selling an iPhone or iPad, log out of Apple ID before you do a factory reset, and remove the device from your list of trusted devices on iCloud, otherwise the legitimate buyer won’t be able to use it.
Chief keyboardist at Asklegal. Don't ask me legal questions. Ask me about the tramp joke instead.